
Meet Your New Digital Workforce: Perplexity Computer
March 27, 2026 / Bryan Reynolds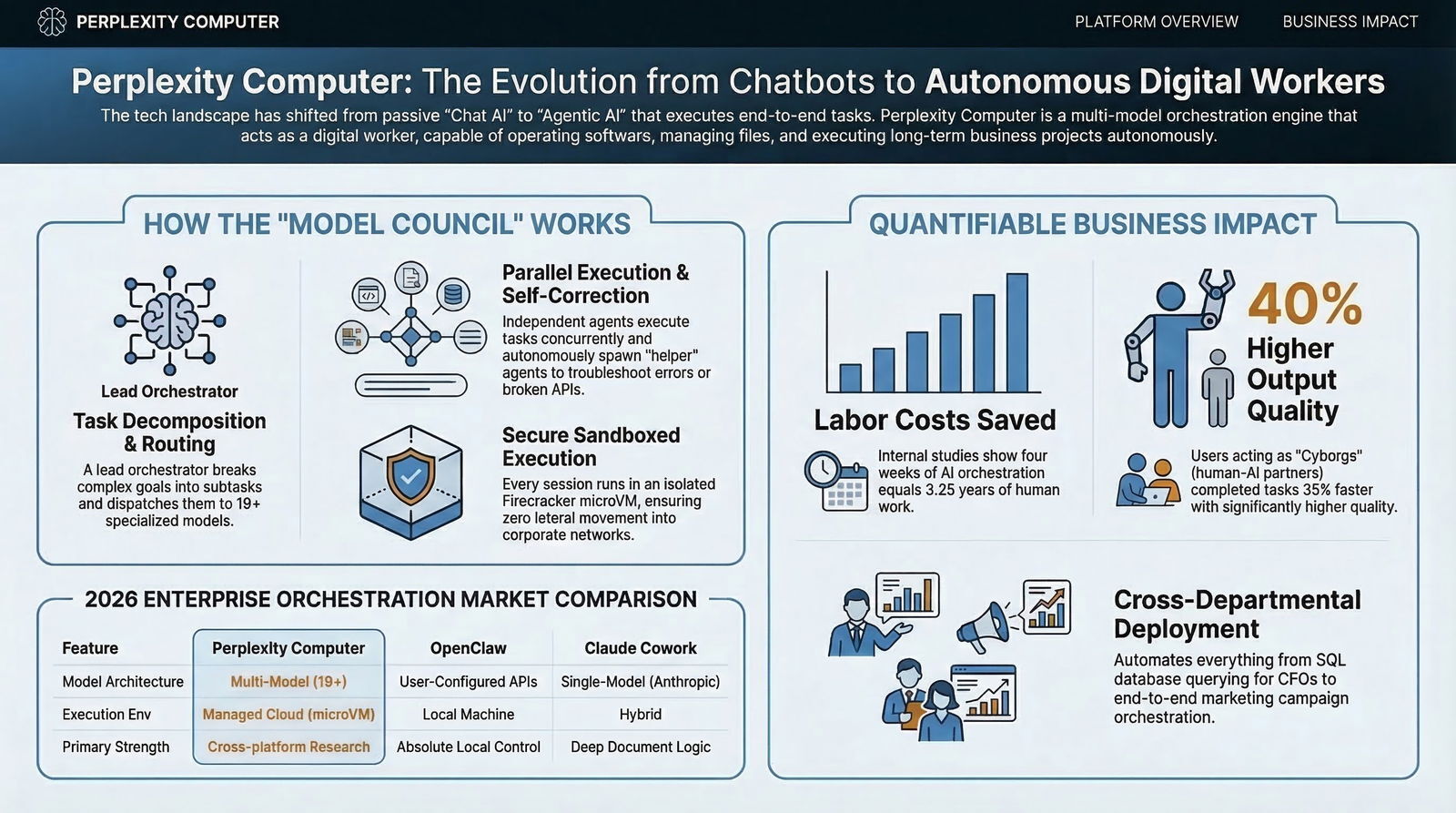
The AI Transformation of B2B Operations: What is Perplexity Computer and How Does It Work?
The enterprise technology landscape has reached a definitive inflection point in the first quarter of 2026. For the past three years, artificial intelligence has primarily functioned within a conversational paradigm: human operators submit queries, and large language models provide text-based responses. While this iteration of artificial intelligence delivered notable productivity gains, it remained fundamentally passive and required constant human intervention to string together complex tasks. The deployment of agentic artificial intelligence has irrevocably altered this dynamic. At the forefront of this shift is Perplexity Computer, a system that transitions machine intelligence from a digital concierge to an autonomous cognitive workforce.
For visionary Chief Technology Officers, strategic Chief Financial Officers, and driven marketing and sales executives, the pressing questions are no longer about the theoretical capabilities of generative models. The current imperatives revolve around operational execution. Specifically, organizations are asking: What exactly is Perplexity Computer? How does its multi-model architecture function in a secure enterprise environment? What are the quantifiable use cases across different business units? How do operators deploy it on a daily basis, and what are the viable alternatives in an increasingly crowded market?
This comprehensive research report provides an exhaustive analysis of Perplexity Computer. It details the platform's architectural framework, its specific enterprise applications, deployment methodologies, and the broader competitive landscape of autonomous orchestration, providing B2B leaders with the strategic data necessary to navigate this technological transition.
Defining the Paradigm Shift: What is Perplexity Computer?
Perplexity Computer is a general-purpose, cloud-based digital worker designed to operate the same software interfaces, digital tools, and file systems utilized by human employees. Introduced to the enterprise market in early 2026, the platform abandons the traditional chatbot interface in favor of an end-to-end workflow execution engine. The foundational premise of the system is concisely articulated by its developers: "Chat answers. Agents do tasks. Computer works".
Unlike conventional tools that rely on a single underlying algorithm, Perplexity Computer is a multi-model orchestration platform. It unifies the capabilities of up to 20 frontier models into a single, cohesive system. The system is capable of understanding a high-level corporate goal, decomposing that goal into a dependency graph of subtasks, navigating across various web applications, and executing workflows that can run autonomously for hours, days, or even months without human oversight.
As organizations move away from simple prompt-based interactions and toward full automation, the definition of what constitutes an "application" is changing. Perplexity Computer effectively treats artificial intelligence as the operating system itself, capable of bridging the gap between raw computational power and finished business deliverables.
The Dual Offerings: Cloud Enterprise and Personal Hardware
The ecosystem exists in two primary deployment formats to serve entirely different operational requirements and security postures within the modern enterprise:
- Perplexity Computer for Enterprise: This is a purely cloud-based orchestration layer that integrates directly into corporate infrastructure. It utilizes secure app connectors to interact with enterprise platforms such as Snowflake, Salesforce, and HubSpot. This version is designed for scalable, organization-wide deployment and is governed by strict administrative controls, Single Sign-On (SSO) frameworks, and zero-data-retention policies. For organizations already standardizing on a strategic .NET AI tech stack, this cloud-first model aligns well with existing security and governance expectations.
- Perplexity Personal Computer: This represents a hardware-integrated solution that runs on a dedicated, continuously operating Mac mini. This version acts as a persistent digital proxy, merging local files with the cloud-based orchestration engine. It operates 24/7, allowing operators to coordinate tasks, execute local scripts, and access native desktop applications remotely from any device, effectively bridging the gap between cloud intelligence and local file management.

How Does Perplexity Computer Work? The Orchestration Engine
To grasp the true utility of Perplexity Computer, one must look beyond the standard generative architecture. The system is built on a proprietary orchestration framework known as the "Model Council," paired with Parallel-Agent Reinforcement Learning (PARL). The fundamental shift here is the abandonment of the "one model to rule them all" philosophy. Industry consensus in 2026 holds that no single monolithic algorithm can excel equally at deep mathematical logic, creative visual generation, low-latency web scraping, and long-form document synthesis.
The Multi-Model Council Architecture
When an operator inputs a complex prompt (for example, "Build an interactive dashboard analyzing the impact of government shutdowns on supply chain logistics using the last twenty years of BLS and FRED data"), the request does not go to a single algorithmic endpoint. Instead, it enters a highly structured, layered pipeline.
- Intent Parsing and Task Decomposition: The central planning engine—currently powered by Anthropic's Claude Opus 4.6—receives the prompt. Known for its superior logical deduction and coding capabilities, Claude Opus acts as the "orchestrator" or "conductor" of the entire operation. It breaks the high-level goal down into a structured task graph, identifying which subtasks must happen sequentially and which can be executed in parallel. This style of orchestration is very similar to the multi-agent patterns described in Baytech’s research on teams of AI agents replacing one “super-bot”.
- Specialized Routing: The orchestrator dispatches these subtasks to a specialized pool of up to 19 different frontier systems.
- Deep Research and Verification: Tasks requiring massive data aggregation and multi-source web traversal are routed to Google's Gemini 3.1 Pro.
- Media and Asset Generation: Requests for visual layouts or motion assets are directed to specialized models like Nano Banana for images and Veo 3.1 for video generation.
- High-Speed Execution: Lightweight, low-latency tasks and rapid data formatting are offloaded to xAI's Grok to conserve high-tier compute resources.
- Long-Context Recall: OpenAI's GPT-5.2 is frequently utilized for managing massive context windows over month-long project timelines, ensuring the system does not lose track of brand guidelines or prior instructions.
- Parallel Execution and Self-Correction: The system initiates dozens of digital agents concurrently. Using PARL infrastructure, these agents work independently across different tools. If a sub-agent encounters a broken API, a deprecated link, or an unexpected software error, it does not halt the entire workflow. Instead, it autonomously spawns a helper agent to troubleshoot the error, rewrite the necessary code, and continue execution.
- Synthesis and Debate: Once the sub-agents complete their tasks, the Model Council framework synthesizes the outputs. In cases of factual ambiguity or contradictory data pulled from the web, multiple models (e.g., Claude, GPT, and Gemini) will independently research a claim, review each other's responses, and flag disagreements in a simulated debate. A designated synthesizer then compiles a highly accurate, citation-backed final deliverable, drastically reducing the risk of algorithmic hallucinations.
Secure Execution Environments and Firecracker microVMs
A critical concern for B2B infrastructure is the safety of executing autonomous code and granting external systems the ability to perform web actions. Organizations cannot risk a rogue process exposing internal networks. Perplexity addresses this by running every Computer session inside an isolated Firecracker virtual machine (microVM).
Originally developed by Amazon Web Services for Lambda serverless computing, Firecracker technology ensures that each query and workflow is perfectly sandboxed. If a digital worker executes malicious code encountered during web research, or if it interacts with a compromised third-party API, the threat is contained entirely within the ephemeral microVM. Once the task is complete, the microVM is destroyed, preventing any lateral movement into the user's local network or Perplexity's broader production servers. This ephemeral architecture is a cornerstone of the platform's SOC 2 Type II compliance and pairs well with the kind of AI firewall and prompt-injection defenses many enterprises now require.
Exhaustive Use Cases: Applications Across the C-Suite
The value proposition of autonomous orchestration is fundamentally different from that of conversational text generation. While previous tools saved minutes on drafting emails or summarizing meeting notes, orchestration engines save weeks on operational execution. In a verified internal study utilizing evaluation metrics aligned with McKinsey, Harvard, MIT, and BCG standards, Perplexity Computer saved internal teams $1.6 million in labor costs by handling 3.25 years' worth of work in a compressed four-week period.
For organizations prioritizing enterprise-grade quality and timely delivery—such as those partnering with specialized custom software development firms like Baytech Consulting—the integration of these tools provides a distinct Tailored Tech Advantage. Below is a detailed breakdown of how different C-suite personas deploy this technology to drive measurable business outcomes.

1. The Visionary CTO: Accelerating Engineering and Infrastructure Management
Technical leaders face mounting pressure to accelerate product deployment while maintaining rigorous security standards and managing complex tech stacks. Perplexity Computer functions as a tireless, autonomous junior engineering team, capable of interacting directly with modern development environments.
- Autonomous Application Development: An operator can prompt the system to build an interactive web application from scratch. The agent will autonomously write the code, debug dependency errors, structure the database, and deploy the application to a live subdomain. In documented testing, the system successfully built complex tools, including Monte Carlo financial simulators and interactive data maps, without any manual human coding. When combined with an AI-native SDLC designed for CTOs, this can move projects from concept to production with far less friction.
- Infrastructure and Deployment Orchestration: When deploying these systems, engineering teams can seamlessly integrate them into existing infrastructure. For example, if a firm is managing on-premise environments via Azure DevOps, orchestrating containerized applications with Docker and Kubernetes, or querying robust databases like Postgres and SQL Server, the Computer can generate the necessary deployment scripts. It can optimize SQL queries for Postgres, draft Kubernetes manifest files, and monitor GitHub repositories for anomalies, executing tasks that typically require hours of manual configuration. Partnering with a firm like Baytech Consulting ensures that this Rapid Agile Deployment is executed securely, with the AI complementing highly skilled human engineers.
- Legacy Code Modernization and Documentation: Technical debt remains a massive hurdle for fast-growing startups and established telecom firms alike. The agent can be directed to scan entire legacy codebases, update technical documentation to modern standards, flag security vulnerabilities based on the latest CVE databases, and generate comprehensive Product Requirements Documents (PRDs) for upcoming sprints. This complements strategies for managing software security, technical debt, and AI governance in complex environments.
2. The Strategic CFO: Financial Modeling and Audit Readiness
Finance departments require absolute precision, making them historically resistant to hallucination-prone generative models. The multi-model verification approach and the ability to cite auditable sources mitigate these risks, enabling high-stakes financial applications.
- Complex Financial Modeling and Forecasting: Analysts can instruct the system to build a 5-year linked 3-statement financial model for a target company or a competitor. The agent autonomously scrapes SEC filings, pulls real-time market data from integrations like FactSet or S&P Global, and assembles the data in a dynamically formatted spreadsheet complete with formulas and growth projections.
- Due Diligence Automation: During Mergers and Acquisitions (M&A), the system acts as an interactive due diligence tracker. It analyzes thousands of documents within a virtual data room, cross-references revenue figures against historical filings, and flags discrepancies, missing clauses, or risk factors for human review. This compresses the due diligence timeline drastically.
- Direct Database Querying for Non-Technical Executives: Using pre-built enterprise connectors, a CFO can ask the system a plain-language question, such as: "What was our vertical revenue growth last quarter compared to the same period last year, and which product lines drove the variance?" The agent translates this natural language into optimized SQL, queries a data warehouse like Snowflake or a local SQL Server directly, and returns a formatted, interactive dashboard. This is an example of moving beyond static reports and killing traditional dashboards in favor of proactive AI that surfaces insights in real time.
3. The Driven Head of Sales: Territory Optimization and Pipeline Management
Sales velocity is heavily dependent on the quality of prospect research and the speed of personalized outreach. The autonomous worker removes the research bottleneck entirely, allowing human representatives to focus on relationship building and closing.
- Deep Lead Enrichment and Briefing Generation: Before a critical demonstration with a high-value enterprise prospect, the agent can conduct a 360-degree review of the target account. It analyzes recent news, executive interviews, product launches, and competitor relationships to build a highly personalized briefing document, highlighting specific pain points the prospect is likely facing.
- Territory and Quota Optimization: The system can consolidate historical performance data from CRM platforms like Salesforce, overlay it with geographic density maps or macroeconomic indicators, and highlight untapped market opportunities within specific sales territories.
- Automated CRM Hygiene and Touchpoint Scaling: By integrating directly with enterprise platforms, the digital worker can listen to call transcripts, extract actionable next steps, draft personalized follow-up emails based on the specific objections raised during the call, and autonomously update CRM records. This eliminates the administrative burden that plagues most sales organizations.
4. The Innovative Marketing Director: Omnichannel Campaign Orchestration
Marketing teams are transitioning from utilizing software solely for copywriting to utilizing it for complete, end-to-end campaign orchestration.
- End-to-End Campaign Creation: A marketing director can provide a core value proposition and a target audience demographic. The agent will independently generate visual ad creatives (utilizing models like Nano Banana), draft optimized social media copy, build A/B tested landing pages, and assemble a performance tracking dashboard to monitor the campaign's success across various channels.
- Sentiment and Trend Analysis: The digital worker can continuously monitor social channels, industry forums, and competitor press releases to identify emerging trends before they become mainstream. It synthesizes these findings into strategic intelligence, advising the marketing team on optimal positioning and messaging adjustments.
- Competitor Benchmarking: The agent excels at running side-by-side feature and pricing analyses against competitors. It can extract verified data from paywalled professional sources like Statista, CB Insights, and PitchBook to uncover unique selling propositions and build comprehensive battle cards for the marketing and sales teams.
Deployment Methodologies: How Do You Use Perplexity Computer?
The interface for interacting with autonomous orchestration requires a fundamental shift in operator behavior. Rather than asking a question and waiting seconds for a static text response, users are essentially delegating projects and managing a digital employee. There are three primary modalities for utilizing Perplexity Computer in a B2B environment:
1. The Slack Integration (Ambient Orchestration)
For many enterprise teams, the primary workspace is not a standalone application, but collaborative platforms like Slack or Microsoft Teams. Perplexity has deeply embedded the Computer within Slack channels.
Users can tag the digital worker directly in a thread, assign a complex task, and proceed with other human-centric work. A prompt might read: "@computer Pull the latest user engagement metrics from our Postgres database, format them into a presentation deck highlighting the key drop-off points, and send it to the product channel." The agent operates asynchronously in the background, spawning necessary sub-agents, writing the queries, and eventually delivering the completed files directly into the Slack channel. This promotes "ambient learning," where team members learn how to prompt and manage the system effectively by observing their colleagues' interactions in public channels.
2. The Comet Enterprise Browser
Recognizing that the vast majority of modern enterprise work occurs within web browsers, Perplexity launched the Comet AI-native browser. Comet understands the context across all open tabs, allowing it to automate repetitive cross-application tasks natively.
If an operator is viewing a candidate's LinkedIn profile in one tab and has an Applicant Tracking System (ATS) open in another, Comet can extract the relevant data and populate the ATS automatically. Through strategic partnerships, such as with CrowdStrike, the browser is secured with enterprise-grade protections. It provides risk scores for installed extensions and safeguards to prevent sensitive corporate information from being inadvertently entered into the assistant or leaked to external servers.
3. The Web Application and Personalized "Skills"
Through the standard Perplexity web application, users can build comprehensive, long-running workflows. A vital feature for maintaining enterprise consistency is the use of customized "Skills." Administrators can program specific instructions that dictate exactly how the system should format data, the desired tone of voice, and the required structure of deliverables. This ensures that a Product Requirements Document generated by the system perfectly matches the organization's unique brand guidelines and standard operating procedures.
Best Practices for Operators:
- Provide Objective-Based Prompts: Instead of dictating highly specific, step-by-step actions that might bottleneck the system, define the final outcome clearly. For example: "I need a compiled list of 50 healthcare logistics startups founded in 2025, ranked by Series A funding, exported as a CSV file."
- Iterative Refinement: After the agent completes the initial workflow, operators should review the output and provide specific feedback. The agent retains session memory and will dynamically correct its work, rewrite code, or adjust formatting without needing to restart the entire process from scratch. This kind of 90/10 collaboration mirrors Human-in-the-Loop models described in Baytech’s work on building trust architecture for AI in 2026.
The Competitive Landscape: Alternatives to Perplexity Computer
The market for autonomous agents is expanding at a staggering rate, with macroeconomic projections indicating growth from $7.63 billion in 2025 to nearly $183 billion by 2033. As enterprise adoption accelerates, B2B executives must rigorously evaluate Perplexity against several formidable alternatives, ranging from open-source frameworks to ecosystem-locked corporate tools.
OpenClaw: The Open-Source Local Challenger
The most frequently cited direct competitor to Perplexity Computer is OpenClaw. Created by Austrian developer Peter Steinberger, OpenClaw approaches agentic workflows from a fundamentally different philosophical and architectural standpoint.
- Architecture and Execution: OpenClaw is an open-source framework that runs locally on the user's hardware rather than in a managed cloud environment. Because it integrates deeply with local operating systems, it possesses unparalleled power to execute local scripts, manage files directly on the hard drive, and interact seamlessly with native messaging applications like WhatsApp, Signal, and Telegram.
- The "Build vs. Buy" Dilemma: OpenClaw represents the ultimate "build" approach. It offers total flexibility for advanced developers who wish to configure their own API keys, orchestrate their own local models, and completely customize the automation pipeline. Perplexity represents the "buy" approach, offering a fully managed, multi-model cloud infrastructure that requires zero setup but operates within the boundaries of its web-based sandboxes.
- Security and Maintenance: Because OpenClaw runs locally and requires manual API integrations, the burden of security, updates, and maintenance falls entirely on the organization's internal IT department. Conversely, Perplexity secures all executions within its cloud-based microVMs, offloading the security risk to the platform provider.
- Performance Differences: OpenClaw is often noted for its speed in executing local file manipulations because it avoids the latency of cloud round-trips. However, Perplexity dominates in broad research, data synthesis, and complex multi-model reasoning.
Claude Cowork (Anthropic)
Anthropic's Claude Cowork relies entirely on the Claude model family, avoiding the multi-model council approach. It excels in environments that require massive context windows and deep, specialized work within a single domain, such as analyzing massive legal codebases, conducting deep compliance checks, or rewriting complex technical manuals. However, because it lacks a diverse orchestration architecture, it struggles with workflows that demand simultaneous visual generation, low-latency web scraping, and varied cognitive models. It is a precision instrument rather than a general contractor.
Microsoft Copilot and Google Gemini 3.1 Pro
The legacy technology giants offer agentic capabilities that are tightly integrated into their respective corporate ecosystems. Microsoft Copilot remains the optimal choice for organizations that are inextricably tied to the Microsoft 365 environment, excelling at manipulating Word documents, generating Excel pivot tables, and summarizing Teams meeting data.
Similarly, Gemini 3.1 Pro dominates within the Google Workspace, offering seamless integration with Google Drive, Docs, and Gmail. However, industry analysts note that these single-vendor solutions often suffer from "ecosystem lock-in." They are highly proficient within their walled gardens but may fail to orchestrate a diverse set of external tools (like Snowflake, Salesforce, or proprietary databases) as seamlessly as an agnostic platform like Perplexity. This is why many enterprises are now focusing on action-oriented agents that can work across systems, not just inside one suite.
Feature Comparison Matrix
The following table provides a concise evaluation of the primary orchestration platforms available in the 2026 enterprise market:
| Feature | Perplexity Computer | OpenClaw | Claude Cowork | Microsoft Copilot |
|---|---|---|---|---|
| Execution Environment | Managed Cloud (MicroVMs) | Local Machine (User Hardware) | Local / Cloud Hybrid | Microsoft Cloud Ecosystem |
| Model Architecture | Multi-Model (19+ orchestrations) | User-Configured APIs | Single-Model (Anthropic) | Single-Model (OpenAI base) |
| Setup & Maintenance | Zero Setup (Turnkey) | High Setup (Developer Required) | Low Setup | Enterprise Integration Required |
| Security Responsibility | Platform Managed (SOC 2 Type II) | User Managed | Platform Managed | Platform Managed |
| Primary Strength | Broad workflow orchestration & cross-platform research | Absolute local control, script execution & speed | Deep document logic, coding, & compliance | Native Microsoft 365 integration & document formatting |
Enterprise Pricing, Cost Management, and Return on Investment
For B2B procurement and financial officers, cost predictability, scalability, and definitive Return on Investment (ROI) are non-negotiable. Perplexity has structured its pricing tiers to accommodate both individual power users and massive, multinational enterprise deployments, ensuring that organizations only pay for the computational resources they require.
The Subscription Tiers (2026 Financial Data)
The platform operates on a per-seat subscription model, segmented by usage limits, security features, and access to the highest-tier reasoning models:
- Perplexity Pro ($20/month or $200/year): Designed for individual professionals and small teams. It offers unlimited standard queries, 20 deep research queries per day, limited file uploads (up to 50 files per space), and access to premium models. However, it lacks the administrative controls, SSO integrations, and security guarantees necessary for corporate deployment.
- Enterprise Pro (40/seat/month or 400/seat/year): The foundational tier for B2B teams. It significantly expands usage limits, offering 500 research queries per day per user. It provides organization-wide file repositories (up to 15,000 files), Single Sign-On (SSO) and SCIM provisioning, and role-based permissions. Crucially, this tier introduces the zero-data-retention and no-training guarantees.
- Perplexity Max (200/month or 2000/year): An individual power-user tier granting unlimited access to the full orchestration of the Computer platform. Subscribers receive priority access to the highest-tier models (like o3-pro and Opus 4.1 Thinking), unlimited Labs projects, and early access to features like the Comet browser.
- Enterprise Max (325/seat/month or 3,250/seat/year): The ultimate B2B tier designed for organizations running massive automated workflows. It provides unlimited deep research, massive file storage limits (5,000 files per Space and 10,000 in the user repository), high-quality audio/video generation, and organization-wide data analytics with no minimum seat requirement.
Token-Based Developer Pricing
For organizations integrating Perplexity's capabilities directly into their own custom software solutions (an area where partners like Baytech Consulting excel), costs are determined by usage metrics rather than fixed monthly seats. The API utilizes token-based pricing:
- Search API: $5 per 1,000 requests for raw web results without synthesized outputs.
- Sonar Pro: $3 per million input tokens, $15 per million output tokens.
- Sonar Deep Research: 2 per million input tokens, 8 per million output tokens, with additional charges for citation generation and search queries.
The ROI Equation: The Harvard and McKinsey Validation
Evaluating the financial impact of agentic orchestration requires looking beyond traditional software subscription costs. A landmark 2026 study conducted by Perplexity in conjunction with researchers from Harvard, utilizing evaluation frameworks from McKinsey, MIT, and BCG, fundamentally challenged the narrative that artificial intelligence is merely a tool for rote administrative chores.
By analyzing hundreds of millions of anonymized interactions, the researchers found that 57% of all agent activity was focused on deep cognitive work—complex research, logic processing, and workflow execution—rather than simple scheduling or email drafting.
The financial implications of this are staggering. In a controlled study of over 16,000 queries, the Perplexity Computer saved internal teams $1.6 million in direct labor costs, executing the equivalent of 3.25 years of cognitive work in only four weeks. Furthermore, a concurrent study by Harvard and BCG on knowledge worker productivity revealed that consultants utilizing advanced models finished 12.2% more tasks, completed them 25.1% faster, and produced results with 40% higher quality compared to control groups. The data indicates that users who act as "Cyborgs" or "Centaurs"—seamlessly moving back and forth between human judgment and machine execution—realize the highest ROI.
Enterprise-Grade Data Governance and Security
Deploying an autonomous agent with broad access to corporate databases, proprietary code repositories, and financial systems requires absolute trust. For B2B enterprises, a security breach orchestrated by an automated system is an existential threat. Perplexity addresses these stringent requirements through a multi-layered compliance and security architecture.
- SOC 2 Type II Certification: The entire Perplexity infrastructure undergoes rigorous, independent auditing to ensure that controls surrounding security, system availability, and data confidentiality are continuously maintained at the highest industry standards.
- Zero Data Retention and No-Training Guarantees: For Enterprise Pro and Enterprise Max clients, the company explicitly guarantees that customer data, uploaded files, query histories, and proprietary code are never used to train their foundational models or shared with third-party LLM partners. The platform is also fully compliant with GDPR, HIPAA, and PCI DSS frameworks.
- Granular Audit Trails: Corporate administrators maintain complete visibility. Every action taken by the digital worker—from API connector usage and file downloads to credit consumption—is captured in the organization's immutable audit logs. This ensures full transparency for internal compliance and regulatory reporting.
- Role-Based Access Control (RBAC): Using SAML SSO and SCIM provisioning, IT departments can restrict which employees have access to specific app connectors. This ensures that the system cannot autonomously pull data from a secure HR database if the user requesting the action lacks the appropriate clearance level, maintaining internal data silos and organizational hierarchies.
- Bug Bounty Programs: To maintain proactive security, Perplexity operates an invite-only bug bounty program through Bugcrowd, rewarding vetted security researchers for identifying and reporting critical vulnerabilities across their web applications, APIs, and cloud services.
Future Outlook: The Agentic Economy
The transition from generative text to autonomous action represents the most significant software evolution since the mass migration to cloud computing. Market analysts at Gartner predict that by the end of 2026, 40% of all enterprise applications will feature task-specific agents, a massive leap from less than 5% in 2025. Furthermore, IDC forecasts that the inference demands driven by agentic usage will grow 1,000x by 2027, triggering a $58 billion market shift that will challenge the legacy productivity tools that have dominated the corporate landscape for three decades.
Organizations that attempt to manually orchestrate individual language models will quickly fall behind competitors leveraging multi-model platforms like Perplexity Computer. The strategic advantage no longer lies in possessing the smartest single algorithm, but in deploying the most efficient, secure, and seamlessly integrated execution layer. This future is closely tied to building an AI “team” of autonomous bots that work alongside humans instead of isolated one-off tools.
Frequently Asked Questions (They Ask, You Answer)
Transparency is critical when evaluating autonomous enterprise technology. Below are direct, unvarnished answers to the most common questions raised by B2B executives evaluating Perplexity Computer.
1. Is our proprietary corporate data secure, and will it be used to train AI models? For Enterprise Pro and Enterprise Max customers, data is strictly sequestered. Perplexity formally guarantees that customer prompts, uploaded files, and connected database queries are entirely excluded from model training, both internally and by their third-party partners. Furthermore, operations are executed within isolated Firecracker microVMs, preventing any data leakage, and the platform adheres to SOC 2 Type II, GDPR, and HIPAA compliance standards.
2. What is the fundamental difference between the Pro and Max tiers? The Pro tier ($20/month) is designed for advanced conversational search and limited daily deep research, acting as a highly intelligent assistant. The Max tier ($200/month for individuals, $325 for enterprise seats) is where true agentic capabilities are unlocked. Max subscribers gain access to the "Computer" orchestration layer, allowing the system to execute autonomous, multi-step workflows in the background, build applications, and utilize the full 19-model council without the strict rate limits applied to the standard Pro tier.
3. Will this technology replace human workers? The current data strongly supports a paradigm of workforce augmentation rather than wholesale replacement. In a massive study conducted by Harvard and Perplexity, 57% of agent activity was classified as complex cognitive work (research, analysis, synthesis) rather than simple administrative tasks. The system acts as a "cognitive partner," compressing the time required for data gathering and initial drafting. This allows human workers to act as editors and strategists, focusing on high-level decision-making, creative problem-solving, and relationship management, ultimately scaling human capability. This aligns with the 90% automation, 10% human oversight model that Baytech outlines in its Human-in-the-Loop trust architecture.
4. How does the system handle factual inaccuracies or "hallucinations"? No system is entirely immune to hallucination, but Perplexity mitigates this risk through its unique "Model Council" architecture. By routing tasks to specialized models and having them cross-verify each other's work against live, cited web data (a process known as Retrieval-Augmented Generation), the system significantly reduces ungrounded outputs. Furthermore, operators maintain control by reviewing the task graph and refining outputs iteratively, keeping a "human in the loop" for high-stakes decisions.
5. How difficult is it to integrate Perplexity Computer with our existing tech stack? The platform is designed for rapid deployment. It features pre-built, secure connectors for major enterprise platforms like Snowflake, Salesforce, Slack, and Microsoft Teams. For custom, on-premise infrastructure, developers can build integrations using the Model Context Protocol or utilize the Perplexity API. However, maximizing the ROI of these integrations often requires specialized software development expertise to ensure data flows securely and efficiently across legacy systems. This is where working with an experienced AI integration partner becomes critical.
Conclusion and Next Steps
Perplexity Computer is not merely an iterative update to a search engine or a chatbot; it is a fundamental restructuring of how digital work is executed. By orchestrating a diverse council of frontier models and executing complex workflows autonomously, it compresses project timelines from weeks to hours. For executives aiming to drive operational efficiency across engineering, finance, sales, and marketing, the integration of autonomous orchestration is rapidly transitioning from a competitive advantage to a baseline necessity.
Successfully deploying these autonomous systems requires more than just purchasing a software license; it demands a strategic alignment of internal data infrastructure, secure deployment pipelines, and custom API integrations. For organizations seeking to harness this tailored tech advantage with enterprise-grade quality and rapid agile deployment, partnering with experts in custom software architecture ensures that these systems integrate flawlessly into existing tech stacks, maximizing ROI while maintaining absolute security. In parallel, leaders should revisit their data foundations to avoid “garbage in, garbage out” scenarios, using data readiness frameworks for enterprise AI to make sure these agents have clean, trustworthy inputs.
About Baytech
At Baytech Consulting, we specialize in guiding businesses through this process, helping you build scalable, efficient, and high-performing software that evolves with your needs. Our MVP first approach helps our clients minimize upfront costs and maximize ROI. Ready to take the next step in your software development journey? Contact us today to learn how we can help you achieve your goals with a phased development approach.
About the Author

Bryan Reynolds is an accomplished technology executive with more than 25 years of experience leading innovation in the software industry. As the CEO and founder of Baytech Consulting, he has built a reputation for delivering custom software solutions that help businesses streamline operations, enhance customer experiences, and drive growth.
Bryan’s expertise spans custom software development, cloud infrastructure, artificial intelligence, and strategic business consulting, making him a trusted advisor and thought leader across a wide range of industries.


