
Agent Wars: OpenClaw vs Perplexity — Who Wins Your Business?
April 24, 2026 / Bryan Reynolds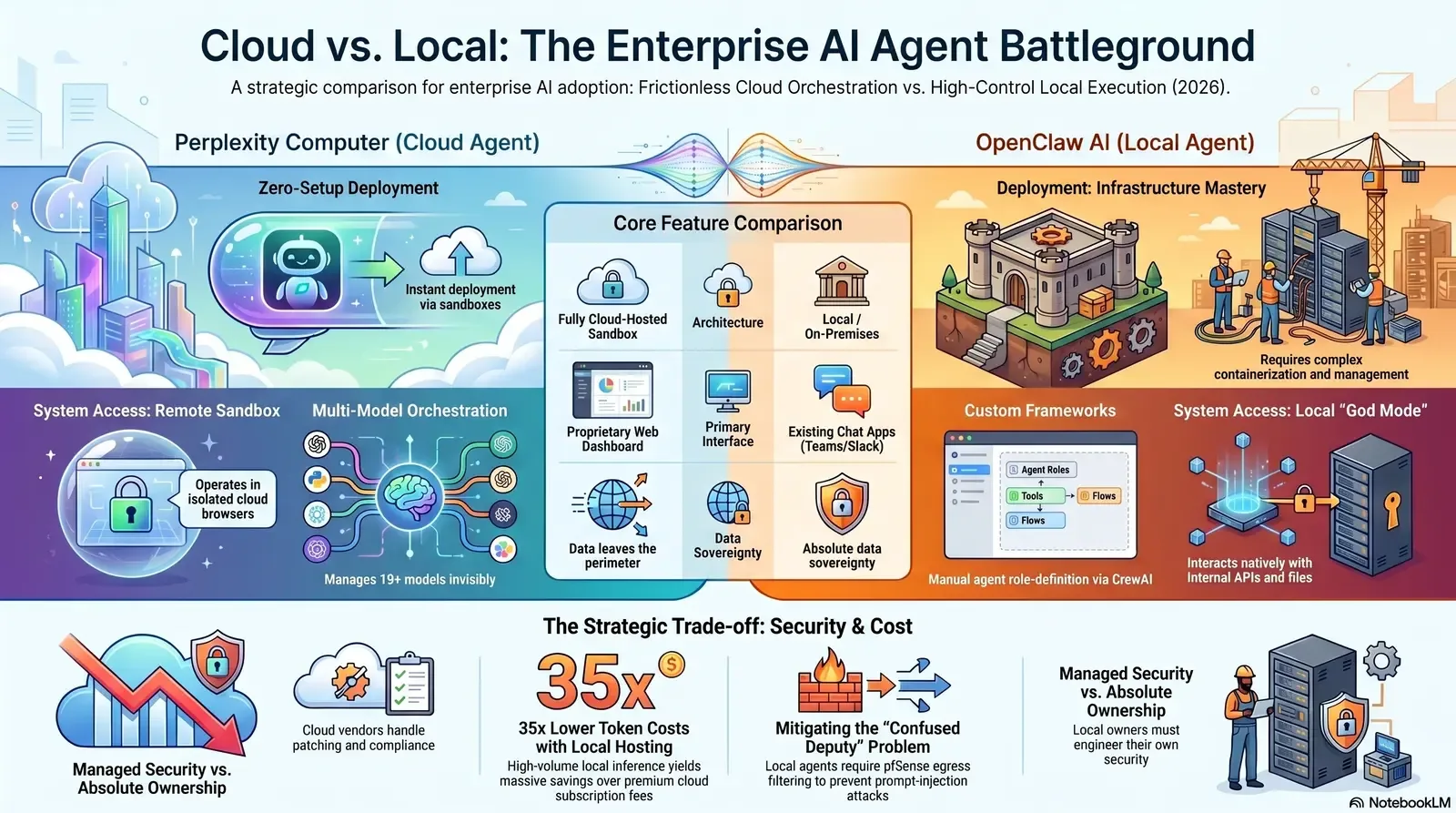
OpenClaw vs. Perplexity Computer: The Local vs. Cloud Agent Debate
At the intersection of enterprise innovation and operational scalability, a critical question is dominating boardroom discussions across B2B sectors: Should organizations deploy open-source, local autonomous agents like OpenClaw within their own infrastructure, or rely on cloud-orchestrated platforms like Perplexity Computer?
In 2026, artificial intelligence has definitively crossed the threshold from conversational assistants that merely generate text to autonomous digital workers capable of executing real-world tasks. These "agentic" systems do not simply answer questions; they plan operations, navigate graphical software interfaces, execute complex multi-step workflows, and operate asynchronously for hours or even months without human intervention. However, as fast-growing startups and B2B enterprises in highly regulated industries like finance, healthcare, software, and advertising race to integrate these capabilities, they face a profound architectural fork in the road.
On one side of the debate is the cloud-based, fully managed paradigm represented by Perplexity Computer. This platform offers seamless multi-model orchestration but demands premium subscription fees—often hitting $200 per user per month—and requires enterprises to trust vendor-controlled cloud sandboxes with their most sensitive intellectual property. On the other side is the self-hosted, open-source model championed by OpenClaw (formerly Clawdbot/Moltbot). OpenClaw promises absolute data sovereignty and significantly lower long-term inference costs, but it requires highly sophisticated infrastructure management to prevent severe enterprise security vulnerabilities.
This exhaustive report analyzes the technical, financial, and security trade-offs between local and cloud-based autonomous AI agents. By evaluating total cost of ownership models, examining the latest OWASP Top 10 for Agentic Applications, and detailing enterprise-grade deployment strategies, this analysis reveals how organizations can harness multi-agent orchestrations securely within their own infrastructure. The objective is clear: to help technology leaders avoid exorbitant cloud overages while maintaining the strict data privacy required in modern B2B environments. For a broader view of how data foundations impact AI success, see our guide on enterprise AI data readiness.
The Evolution of Autonomous Enterprise AI
To comprehensively evaluate the debate between OpenClaw and Perplexity Computer, one must first examine the structural shift in how artificial intelligence interacts with enterprise ecosystems. Traditional large language models (LLMs) operate as stateless inference engines: a prompt is provided, an output is generated, and the interaction immediately ends. The system retains no memory of the event outside of a limited context window, and it possesses no inherent ability to alter the state of the user's computer or external software.
Autonomous agents represent a fundamentally different computational architecture. They operate continuously as long-running backend services, maintain persistent state across multiple sessions, dynamically orchestrate external tools, and execute workflows based on intermediate reasoning loops. This continuous "perceive, reason, act, evaluate" cognitive loop allows agents to independently navigate web interfaces, read and write files, generate and execute terminal commands, and respond to unpredictable errors dynamically.
The Strategic Stakes for B2B Executives
For the modern executive suite—the visionary Chief Technology Officer (CTO), the strategic Chief Financial Officer (CFO), the driven Head of Sales, and the innovative Marketing Director—the deployment of autonomous agents is not merely an IT infrastructure upgrade; it is a structural transformation of the digital workforce. Agents are now highly capable of autonomously managing financial data pipelines, parsing massive datasets, auditing internal CRM systems, and orchestrating entirely automated outbound marketing campaigns.
However, with this unprecedented autonomy comes unprecedented enterprise risk. Security professionals refer to the "lethal trifecta" of AI agent risk: direct access to private enterprise data, continuous exposure to untrusted external content, and the delegated authority to act on a human user's behalf. If an autonomous agent is compromised through a malicious prompt or a faulty internal logic loop, it possesses the capability to exfiltrate sensitive data or execute unauthorized, destructive actions at machine speed. Consequently, the choice between adopting a vendor-managed cloud service and engineering a self-hosted local agent becomes a pivotal, foundational decision regarding enterprise risk management, infrastructure investment strategy, and long-term total cost of ownership. To dig deeper into how to measure and manage the impact of this new AI-powered workforce, you may also want to review our playbook on developer productivity metrics that matter.
Deep Dive: Perplexity Computer (The Cloud Orchestrator)
Perplexity Computer represents the current apex of the managed, cloud-orchestrated agentic paradigm. It is positioned by its developers not merely as a software application, but as a "general-purpose digital worker" that operates the exact same graphical and programmatic interfaces that human employees use.
Advanced Multi-Model Orchestration
Unlike single-model systems that rely entirely on one proprietary LLM, Perplexity Computer utilizes an intelligent multi-model orchestration framework, dynamically routing specific tasks to the frontier models best suited for those distinct functions. When a marketing director or a financial analyst delegates a complex workflow—such as conducting deep competitive market research, compiling the resulting data into an interactive spreadsheet, and drafting an executive summary for the board—the system automatically breaks down the prompt and spawns specialized sub-agents.
In 2026, this sophisticated orchestration leverages a proprietary suite of over 19 distinct models simultaneously, seamlessly including:
- Opus 4.6: Functioning as the core reasoning, planning, and executive logic engine.
- Gemini: Deployed specifically for deep, wide-scale internet research tasks and the creation of subsequent sub-agents.
- Nano Banana & Veo 3.1: Utilized exclusively for complex image and video processing generation, respectively.
- Grok: Tapped dynamically for the high-speed execution of lightweight, low-latency administrative tasks.
- ChatGPT 5.2: Used heavily for broad search queries and long-context documentation recall.
This intricate coordination is fully automated and entirely asynchronous. If the Perplexity agent encounters an unexpected roadblock during execution—such as a broken URL, a missing API key, or a dynamically changing website layout—it reasons through the problem, attempts alternative navigation paths, or independently writes temporary code to bridge the gap. It only pauses to alert the human user if it absolutely requires manual authentication or high-level strategic authorization.

Cloud Sandboxing and Frictionless Deployment
The primary operational appeal of Perplexity Computer for non-technical B2B users and heavily siloed departments is its frictionless deployment model. Zero local infrastructure setup is required. The entire system executes tasks within a highly isolated, vendor-managed, cloud-hosted compute environment complete with its own virtual file system and a headless virtual browser.
The AI agent "sees" web interfaces exactly as a human employee does, reading pixels on screens, deciding which buttons to click, typing inputs into forms, and handling multi-step interactive sequences entirely on remote servers rather than on the user's local corporate endpoint. For organizations prioritizing rapid speed to value, this architecture means that employees can begin delegating heavy operational tasks—such as automated data collection, bulk form processing, and continuous competitor analysis—immediately. This entirely bypasses the need for engineering teams to provision physical servers, manage complex OAuth tokens, or maintain a constantly evolving software infrastructure. If you're exploring how to turn this kind of automation into real operational leverage, our guide on AI automation that actually works provides additional context.
Deep Dive: OpenClaw AI (The Local Powerhouse)
Standing in stark architectural contrast to Perplexity's closed, vendor-managed ecosystem is OpenClaw. OpenClaw (previously known in its earlier iterations as Clawdbot, Moltbot, and Molty) is a free, open-source autonomous AI agent framework designed from the ground up for maximum extensibility and local-first execution. Operating natively across macOS, Linux, and Windows environments, it has rapidly gained immense traction among developers and enterprise architects, amassing over 160,000 GitHub stars by early 2026.
Architectural Freedom and Extensibility
Unlike Perplexity Computer, which confines execution to a cloud sandbox, OpenClaw connects large language models directly to the user's real software and local network infrastructure. Instead of operating in a remote virtual browser, OpenClaw runs directly on the user's hardware or an enterprise's self-hosted servers. This direct access grants the agent the ability to interact natively with the local file system, execute powerful terminal commands, and securely control internal corporate APIs that are not exposed to the public internet.
Its user interface is highly adaptive and omnichannel, allowing employees to trigger complex automation workflows directly from the secure messaging platforms they already use daily, such as Slack, Microsoft Teams, WhatsApp, and Telegram, as well as via a dedicated macOS menu bar companion application.
At the very core of OpenClaw's capability is its modular "Skills" system. Skills are isolated directories containing specific SKILL.md metadata files and detailed execution logic that explicitly teach the agent how to interact securely with specific applications. With over 100 robust built-in skills and a thriving community-driven marketplace known as ClawHub, enterprise developers can tightly integrate OpenClaw into proprietary legacy systems. This allows the agent to seamlessly query internal databases and interact with custom middleware—deep integrations that are often structurally impossible or prohibitively dangerous when attempted with a standardized, external cloud vendor. For many organizations, this is the same philosophy that underpins sidecar-style modernization approaches, like those described in our article on AI sidecars for legacy systems.
| Feature Dimension | Perplexity Computer | OpenClaw AI |
|---|---|---|
| Deployment Architecture | Fully Cloud-Hosted Sandbox | Local, On-Premises, or Self-Hosted |
| Model Dependency | Multi-Model (Vendor Selected) | Model Agnostic (User Selected) |
| Infrastructure Setup | Zero setup required | Requires containerization & network routing |
| Local System Access | None (Operates in cloud virtual machine) | Full (Terminal, local files, internal APIs) |
| Primary Interface | Proprietary Web Dashboard / Browser | Existing Chat Apps (Teams, Slack, CLI) |
The Infrastructure Imperative for B2B Operations
The raw power of OpenClaw comes inextricably linked with the heavy burden of technical complexity. It is emphatically not a plug-and-play solution for the enterprise. While viral developer marketing often highlights its ease of use for hobbyists, running OpenClaw safely and effectively in a B2B production environment requires significant dedicated engineering resources. Organizations must actively manage local Node.js environments, interactive deployment wizards, secure OAuth gateways, API key rotations, and highly restricted execution sandboxes to prevent catastrophic system errors.
However, for technically sophisticated engineering teams and organizations leveraging specialized application management providers, this complexity is not a deterrent but a distinct competitive advantage. It allows for a tailored tech advantage. By utilizing modern containerization protocols and robust orchestration platforms, enterprises can transform OpenClaw from a fragile desktop novelty into a highly resilient, enterprise-grade backend automation service.
The Core Debate 1: Enterprise AI Security & Data Privacy
The most critical and heavily scrutinized battleground in the local versus cloud agent debate is enterprise security. Autonomous agents introduce unprecedented risk vectors because they possess the actual agency to act, transforming traditional read-only data breaches into scenarios of active network sabotage or catastrophic, high-speed system errors.
The Security Implications of Cloud Orchestration (Perplexity)
Perplexity Computer significantly mitigates local endpoint risk by strictly confining all execution and reasoning to its proprietary cloud infrastructure. Because the agent operates a remote virtual browser, it physically never touches the enterprise's local files, internal network architecture, or end-user laptops. This architectural decision creates a massive reduction in the local attack surface, effectively neutralizing the risk of an agent accidentally deleting local databases or downloading malware onto a corporate workstation.
Furthermore, Perplexity Computer for Enterprise is heavily fortified by centralized, enterprise-grade security protocols. These include SOC 2 Type II certification, strict GDPR and HIPAA compliance frameworks, Single Sign-On (SAML SSO and SCIM) integrations for identity management, detailed audit logs, and highly configurable file retention policies. The vendor centrally manages all complex model routing, software updates, and zero-day vulnerability patching, significantly alleviating the day-to-day burden on internal IT and security teams.
However, this managed architecture requires an absolute, non-negotiable transfer of trust. The enterprise must routinely transmit its sensitive intents, proprietary data, and internal API keys (if connecting to external SaaS tools) directly to Perplexity's servers. While Perplexity guarantees via strict service level agreements that enterprise data is never used to train its base LLMs, the fundamental reality remains: the data still leaves the organization's secure perimeter. For highly regulated industries dealing with classified intellectual property, stringent data residency requirements, or sensitive healthcare records, this externalization of data processing is often a fundamental non-starter. In those situations, security teams should also evaluate patterns like an AI firewall for prompt-injection defense to further harden their architecture.
The Security Implications of Self-Hosted Agents (OpenClaw)
Deploying OpenClaw entirely on-premises provides the ultimate solution to the data privacy dilemma: absolute data sovereignty. All agent telemetry, user prompts, execution logs, and intermediate reasoning steps remain entirely within the enterprise firewall, fully satisfying the strictest global compliance mandates and data residency laws. However, the local execution model introduces severe internal vulnerabilities if it is improperly managed or deployed casually by end-users.
By its very nature, OpenClaw inherently requires broad system access to function effectively. If deployed carelessly on an individual developer's laptop or an unsegmented corporate server, the agent operates with effectively "God Mode" privileges. An unconstrained agent could theoretically read highly classified SSH keys, modify production source code, or exfiltrate massive databases at machine speed.
The global cybersecurity research community has repeatedly flagged these immense risks. The recently published OWASP Top 10 for Agentic Applications 2026 highlights several critical vulnerabilities pertinent to self-hosted frameworks like OpenClaw:
- Agent Behavior Hijacking (Prompt Injection): External, untrusted data (such as a malicious string of text hidden invisibly in a website the agent is researching) can inject hostile instructions that completely override the agent's core directives, turning it into a "Confused Deputy" acting on behalf of a threat actor.
- Tool Misuse & Exploitation: If an agent is granted overly broad permissions, attackers can trick the logic model into using legitimate tools maliciously, such as formatting a critical network drive or silently emailing highly sensitive financial documents to an external server.
- Identity & Privilege Abuse: Autonomous systems can seamlessly inherit human permissions or access cached credentials, unintentionally escalating privileges beyond their required scope.
Cisco security researchers recently demonstrated the severity of these risks, proving that third-party skills installed via OpenClaw's public ClawHub marketplace were fully capable of performing background data exfiltration without any user awareness. Furthermore, default OpenClaw installations store crucial context files, such as MEMORY.md and SOUL.md, alongside sensitive API keys in plaintext, creating an incredibly lucrative token goldmine for any attackers who manage to breach the perimeter.
Engineering a Secure OpenClaw Environment: The Technical Blueprint
To effectively mitigate these severe risks, B2B enterprises cannot simply download OpenClaw, install it on a desktop, and walk away. They must actively engineer a rapid, agile deployment utilizing advanced, enterprise-grade infrastructure paradigms. A best-in-class enterprise architecture for OpenClaw relies heavily on rigorous network segmentation and strict access controls.
1. Virtualization and Kubernetes Orchestration Instead of running OpenClaw natively on bare metal servers or vulnerable user endpoints, organizations must utilize robust hyperconverged infrastructure. By leveraging platforms like Harvester HCI, engineering teams can provision deeply isolated virtual machines specifically designed for agent workloads. These VMs are then managed via Rancher to deploy a highly resilient, scalable Kubernetes cluster.
By fully containerizing the OpenClaw runtime environment using Docker and deploying it via custom Helm charts, the autonomous agent is physically restricted to a strictly defined Kubernetes namespace. It is granted kubectl access exclusively to its own sandboxed environment, allowing it to spin up temporary, ephemeral pods for specific execution tasks without ever gaining the ability to touch or modify the broader enterprise cluster. Read-only file systems must be enforced by default, forcing the agent to write its state solely to designated Persistent Volume Claims (PVCs), eliminating the risk of it overwriting critical system files.
2. pfSense Egress Filtering and Threat Mitigation One of the most critical, yet frequently overlooked, security controls for a self-hosted agent is comprehensive egress filtering. Because OpenClaw integrates directly with web browsers and external APIs to perform its duties, a compromised agent could easily attempt to exfiltrate proprietary data to a malicious command-and-control server.
By routing all OpenClaw container traffic directly through pfSense firewalls, enterprises can implement a strict "Default Deny" outbound policy. Egress traffic is heavily restricted via explicit allowlists, utilizing STRICT_ORDER evaluation to permit communication only with verified, pre-approved enterprise domains, whitelisted LLM API endpoints, and necessary internal SaaS platforms. This architecture ensures that even if an OpenClaw agent falls victim to an indirect prompt injection attack—perhaps from reading a poisoned competitor's website—it is physically incapable of transmitting any stolen data to unauthorized external IP addresses.
3. Integrating the Enterprise Tech Stack When secured correctly, this infrastructure enables seamless and safe integration with the broader corporate environment. A properly sandboxed OpenClaw agent can securely query a localized Postgres database or an SQL Server, format the analytical results using localized Python execution environments, and commit the final code through Azure DevOps On-Prem, or upload the generated reports directly to an enterprise Microsoft 365/OneDrive instance. Development and continuous integration of the agent's logic can be maintained efficiently using standard tools like VS Code and VS 2022, ensuring that the AI remains a tightly controlled asset rather than a rogue shadow IT liability. For a complementary pattern on modernizing older systems around this kind of architecture, see how we use non-invasive overlays in our article on giving legacy systems a voice with AI.
The Core Debate 2: Cost Analysis & Avoiding the Cloud Overage Trap
The financial models for deploying cloud-based versus self-hosted autonomous agents diverge significantly as enterprise utilization scales. While the initial barrier to entry heavily favors managed SaaS solutions, the long-term total cost of ownership (TCO) tells a drastically different story for the strategic CFO.
The True Cost of Perplexity Computer
Perplexity's pricing model is expertly designed for frictionless, rapid adoption across enterprise teams, but it can become severely punitive at a large operational scale. Access to the full suite of Perplexity Computer capabilities requires the "Enterprise Max" tier (or equivalent individual Max tiers). While base-level Pro tiers run approximately $20 per month, true agentic workflows—which utilize the highest usage limits, longest compute times, and the most advanced frontier models—require the Max subscription, pushing baseline costs toward $200 per user, per month.
For a mid-sized B2B enterprise deploying the agent to 100 core employees, this baseline subscription alone constitutes a $240,000 annual operational expense (OpEx). However, the hidden financial danger lies in consumption-based API limits and unpredictable overages.
Autonomous agents are inherently stochastic and unpredictable. When they encounter unexpected errors, they can enter infinite reasoning loops, rapidly burning through query limits and compute credits as they repeatedly try and fail to solve a problem. A documented industry case study highlighted an agent tasked with building a web application that encountered a silent error during an npm install within the vendor's cloud sandbox. Unable to diagnose the invisible error, the agent engaged in a compounding feedback loop, pushing broken software builds to a repository and burning through 10,000 usage credits before a human administrator noticed and intervened.
Because the end-user has absolutely zero control over the underlying infrastructure or the retry logic implemented by Perplexity's black-box orchestrator, they are entirely exposed to the financial impact of these cascading failures. As AI usage scales, this lack of cost governance becomes a primary concern for financial executives monitoring software spend volatility.
| Cost Component | Perplexity Computer (SaaS) | OpenClaw AI (Self-Hosted) |
|---|---|---|
| Licensing Fee | ~$200/user/month (Enterprise Max) | Free (Open Source MIT License) |
| Infrastructure Setup | $0 | High initial engineering hours (CapEx) |
| Ongoing Compute | Included in subscription limits | Variable based on local server load (OpEx) |
| LLM Inference | Included in subscription limits | API usage fees (or near-zero if running local open-source models) |
| Overage Risk | High (Stochastic reasoning loops burn credits) | Low (Internally controlled token limits) |
The Economics of Self-Hosted AI
OpenClaw completely flips this economic model. The software framework itself is open-source and free, meaning there are absolutely zero per-seat licensing costs, regardless of how many employees utilize the system. The financial burden shifts entirely from recurring subscription fees to infrastructure compute (CapEx) and LLM API inference costs (OpEx).
For small pilot programs, self-hosting can initially appear more expensive due to the upfront engineering hours required to configure the Rancher Kubernetes clusters, deploy pfSense firewalls, and establish storage integrations. A custom middleware layer and self-hosted agent setup might cost 300 to 1,200 monthly in basic compute and API fees for a small team, excluding the initial development time required for deployment.
However, as of 2026, the transition to high-throughput inference has fundamentally altered the TCO calculus for large organizations. The introduction of ultra-efficient, localized hardware—such as NVIDIA Blackwell architectures hosted on dedicated OVHCloud servers or on-premise racks—allows enterprises to run advanced open-source models (like Llama 3 or Mistral) directly on their own Harvester HCI clusters.
NVIDIA's token economics framework clearly demonstrates that self-hosting high-volume inference yields up to a 35x lower cost per million tokens compared to relying exclusively on premium Model-as-a-Service APIs from major vendors. For enterprises processing millions of automated agentic workflows daily—such as mass B2B lead generation, continuous codebase refactoring, or real-time tier-1 support triage—the self-hosted model achieves a definitive financial breakeven point in under four months. This model completely eliminates the risk of cloud vendor lock-in and protects the organization against unpredictable mid-contract subscription tier shifts.

The Core Debate 3: Multi-Agent Orchestration & Control
As AI workflows mature, they rapidly expand beyond the capabilities of a single agent. The final architectural battleground lies in how these systems handle complex, multi-faceted tasks that require distinct types of reasoning, deep collaboration, and specialized roles.
The Platform Approach: Perplexity Computer
Perplexity utilizes a strict "Platform" orchestration approach. In this model, the end-user does not define the individual sub-agents, assign their specific roles, or map out their interaction protocols. The user simply provides the final objective in natural language, and the platform's proprietary backend takes full control—spawning, coordinating, and resolving conflicts between the various sub-agents invisibly in the background.
This opaque, black-box approach is highly efficient for generalist tasks that do not require strict regulatory oversight, such as generating automated weekly intelligence briefings, conducting deep internet research on market trends, or building simple interactive data dashboards from public information. However, the total lack of operational transparency means the enterprise cannot audit the internal logic chain. If the Perplexity agent makes a poor strategic decision midway through a workflow, the user has absolutely no capacity to view the intermediate steps, adjust the sub-agent's specific prompt, or alter the reasoning framework to prevent future errors.
The Framework Approach: OpenClaw and CrewAI
OpenClaw approaches complex multi-agent orchestration from an entirely different, highly modular philosophy. OpenClaw itself is not explicitly a multi-agent collaboration framework; rather, it is an automation infrastructure layer. Its primary strength is deterministic execution: ensuring that once an AI makes a decision, that exact action is applied consistently, securely, and reliably across real-world tools, local databases, and enterprise APIs.
For sophisticated multi-agent reasoning, OpenClaw is frequently paired with specialized orchestration frameworks like CrewAI or OpenAI Swarm. CrewAI operates as the "intelligence and coordination layer," allowing software developers to explicitly define role-based agents (for example, creating a strict "Senior Data Analyst" agent and an adversarial "Quality Assurance" agent), map out their delegation protocols, and carefully structure their reasoning loops.
When these systems are combined in production, CrewAI handles the high-level cognitive work—debating strategies, refining data, and determining the optimal solution through collaborative teamwork. Once a consensus is reached, OpenClaw takes the finalized decision and executes it securely across the enterprise's local applications. In the most advanced enterprise deployments of 2026, this integration is increasingly managed by stacks like NVIDIA NemoClaw, which provides a highly secure runtime environment (OpenShell) specifically optimized for these complex, self-evolving multi-agent architectures.
This highly modular approach grants organizations total, granular control over their AI workforce. They can audit the exact communication logs between internal agents, strictly enforce mandatory human-in-the-loop approvals for high-impact actions (a core recommendation from the OWASP foundation), and seamlessly swap out the underlying LLMs based on fluctuating API costs or evolving privacy requirements without ever needing to rebuild the execution pathways. For sales and go-to-market teams, the same orchestration ideas show up in domain-specific systems like our AI sales engineer / RFP automation architecture.
Conclusion: Which Autonomous Agent Model Best Protects Sensitive B2B Data?
The verdict on whether to deploy a vendor-managed, cloud-orchestrated powerhouse or a self-hosted, local autonomous agent ultimately hinges on the organization's technical maturity, financial structure, and regulatory environment.
For highly regulated B2B enterprises—spanning finance, healthcare, defense, and high-tech software development—the self-hosted, open-source model represented by OpenClaw is undeniably superior for protecting sensitive corporate data. By keeping all telemetry, contextual prompts, and data execution strictly within the enterprise firewall, organizations completely neutralize the immense risks of third-party data exposure, unauthorized vendor training, and restrictive vendor lock-in. The ability to audit every action and tightly control infrastructure makes it the only viable choice for strict compliance environments.
However, it is vital to recognize that "open-source" does not inherently mean "secure." Deploying OpenClaw safely requires transcending casual, plug-and-play desktop installations. It demands a robust, enterprise-grade infrastructure. Organizations must containerize the agent via Docker, deploy it on hyperconverged infrastructure like Harvester HCI, manage it through Kubernetes for strict namespace sandboxing, and enforce rigorous egress filtering via pfSense firewalls to actively prevent rogue behavior and data exfiltration.
Conversely, for fast-growing startups or heavily siloed departments operating entirely outside of strict regulatory compliance—where speed to market, lack of engineering overhead, and ease of use outrank absolute data sovereignty—Perplexity Computer remains an exceptionally polished and powerful tool. It provides unparalleled, instant access to a suite of frontier models without the heavy burden of infrastructure management, albeit at the distinct risk of rapidly escalating monthly subscription costs and the inherent vulnerabilities of transferring data to a cloud sandbox. If you are comparing broader AI platform options and where to invest next, it may also help to read our overview of Perplexity Computer as a digital workforce.
Next Steps for Enterprise Integration
For B2B enterprises seeking to harness the immense power of OpenClaw without succumbing to the severe complexities of DIY infrastructure management, partnering with specialized application management providers is the optimal, risk-averse path forward. A strategic, secure deployment should include:
- Comprehensive Infrastructure Auditing: Evaluate all current on-premises capabilities (such as Azure DevOps On-Prem and OVHCloud servers) to ensure they can adequately support persistent, stateful agent runtimes without performance degradation.
- Containerized Agile Deployment: Transition immediately from local bare-metal execution to orchestrated Docker and Kubernetes environments managed seamlessly by Rancher, ensuring all autonomous agents operate within securely restricted, heavily monitored namespaces.
- Rigorous Network Hardening: Implement strict, OWASP-aligned network controls, prioritizing explicit allowlists and comprehensive pfSense egress filtering to mitigate the catastrophic risks of prompt injection and outbound data exfiltration.
Related Resources
- https://www.cyberark.com/resources/blog/how-autonomous-ai-agents-like-openclaw-are-reshaping-enterprise-identity-security
- https://genai.owasp.org/resource/owasp-top-10-for-agentic-applications-for-2026/
- https://lenovopress.lenovo.com/lp2368-on-premise-vs-cloud-generative-ai-total-cost-of-ownership-2026-edition
Frequently Asked Questions
What are the specific security implications of running an open-source agent like OpenClaw on-premises versus in the cloud? Running an open-source agent like OpenClaw on-premises grants absolute control over your data, ensuring it never leaves the corporate firewall. However, the primary implication is that the burden of securing the agent shifts entirely to your internal IT team. Because OpenClaw requires broad access to local files and terminals to execute tasks, a poorly secured installation can lead to "God Mode" privilege escalation, where the agent could alter code or access sensitive databases. In contrast, cloud agents like Perplexity operate in isolated vendor sandboxes; while this protects your local network, it requires sending your sensitive data and intents to a third-party server, creating severe compliance and data residency implications.
How does Perplexity Computer's cloud orchestration compare to self-hosted AI workflows in terms of cost and control? Perplexity offers an incredibly smooth, zero-setup platform experience but at a premium SaaS price, typically demanding the $200/month Enterprise Max tier for true agentic capabilities. Crucially, the cost is unpredictable due to usage limits and the risk of the agent burning credits in infinite reasoning loops. You also have zero control over which models are routed to which tasks in the background. Self-hosted workflows require significant upfront CapEx (engineering time and server infrastructure) but boast near-zero marginal OpEx. Furthermore, self-hosting gives you total control over the orchestration framework, allowing you to pair OpenClaw with tools like CrewAI to define specific agent roles, audit their logic, and manually approve high-impact actions. For organizations trying to keep AI bills in check more broadly, our cost-focused guide on reducing the token tax on LLMs outlines additional patterns like routing and caching.
What are the specific risks of prompt injection in autonomous agents like OpenClaw? Prompt injection in traditional, read-only chatbots usually results in the model outputting offensive or factually incorrect text. In an autonomous agent like OpenClaw, which has active access to external tools and system files, a prompt injection is far more severe. It triggers what security professionals call the "Confused Deputy Problem." If an attacker hides a malicious command inside a webpage the agent is actively researching, the agent may interpret that command as a legitimate instruction from the user. Because the agent possesses elevated system permissions, it could unwittingly execute unauthorized actions, such as emailing sensitive internal corporate documents to an external server or silently altering local databases. For many teams, a dedicated AI compliance bot layer adds another safeguard to catch risky behavior before it reaches production.
How does pfSense egress filtering prevent AI data exfiltration? Egress filtering controls the specific network traffic leaving your local corporate network. A self-hosted agent like OpenClaw should always be placed behind a pfSense firewall configured with a strict "Default Deny" policy for outbound traffic. IT security teams must manually create an explicit allowlist (using STRICT_ORDER evaluation) that only permits the agent to communicate with highly specific, necessary domains (like the OpenAI API endpoint or an internal CRM system). If the agent is compromised via prompt injection and attempts to send data to an unauthorized, attacker-controlled IP address, the firewall will automatically block the connection, preventing any data exfiltration.
About Baytech
At Baytech Consulting, we specialize in guiding businesses through this process, helping you build scalable, efficient, and high-performing software that evolves with your needs. Our MVP first approach helps our clients minimize upfront costs and maximize ROI. Ready to take the next step in your software development journey? Contact us today to learn how we can help you achieve your goals with a phased development approach.
About the Author

Bryan Reynolds is an accomplished technology executive with more than 25 years of experience leading innovation in the software industry. As the CEO and founder of Baytech Consulting, he has built a reputation for delivering custom software solutions that help businesses streamline operations, enhance customer experiences, and drive growth.
Bryan’s expertise spans custom software development, cloud infrastructure, artificial intelligence, and strategic business consulting, making him a trusted advisor and thought leader across a wide range of industries.


