
Executive Guide: Why DevSecOps Is Now Essential for Security and Growth
October 22, 2025 / Bryan Reynolds
DevSecOps Is Now Essential: An Executive's Guide to Secure Growth and Risk Mitigation
As a business leader, you're caught between two powerful currents: the demand to innovate and deploy faster than ever, and the rising tide of cyber threats that grow more sophisticated by the day. For years, the standard approach to software security was a final, slow checkpoint at the end of the development cycle—a "bolted-on" process that created bottlenecks, frustrated development teams, and ultimately, left businesses exposed. That model is no longer viable.
Welcome to the era of DevOps and DevSecOps. Far more than a technical buzzword, DevSecOps—short for Development, Security, and Operations—is a strategic framework and a cultural shift. It's about integrating security into every single stage of the software development lifecycle (SDLC), from the initial idea to the final deployment and beyond. The core principle is simple but transformative: security is a shared responsibility, not a task relegated to a siloed team.
This is achieved through a concept known as "shifting left." Imagine your development process as a timeline from left to right, with the final product release on the far right. Historically, security checks happened at the very end. Shifting left means moving those security activities to the very beginning of the timeline. This proactive approach allows teams to identify and fix vulnerabilities early in the process, when they are exponentially cheaper, faster, and easier to resolve.
This report is designed to answer the four fundamental questions on every business owner's mind when it comes to this critical evolution:
- What should we be doing right now?
- What are the real risks of doing nothing?
- Where have others failed, and what can we learn?
- What tools and practices actually work?
Your Action Plan: What Business Owners Must Do Now
Embarking on a DevSecOps journey is a strategic initiative that requires more than just a new suite of software. It demands a fundamental change in how your organization thinks about, builds, and delivers value. The most successful transformations are not dictated by technology but are led by a clear vision and a structured, manageable approach.
It Starts with Culture, Not Code
The most common mistake organizations make is approaching DevSecOps as merely a set of tools to purchase and implement. In reality, the practice is 80% culture and process, and only 20% tools. The real transformation is one of mindset.
- Secure Leadership Buy-In: A successful DevSecOps initiative is impossible without strong, visible support from the top. Leadership plays a vital role in setting the tone, securing the necessary resources, and driving organizational commitment. It is the executive team's responsibility to champion the vision that security is not a cost center or a roadblock, but a critical business enabler that protects revenue and builds customer trust.
- Break Down the Silos: For decades, development, security, and operations teams have worked in separate, often adversarial, silos. Developers were incentivized to build fast, operations to maintain stability, and security to say "no." DevSecOps systematically dismantles these walls, uniting these traditionally separate roles into a single, collaborative team with a shared responsibility for delivering software that is both fast and secure. This fosters empathy and eliminates the counterproductive finger-pointing that plagues traditional models.
- Empower Security Champions: A powerful and practical first step is to identify and empower "Security Champions" within your development teams. These are engineers with a passion for security who receive additional training and act as the first line of defense. They serve as a crucial bridge between the central security team and the developers on the ground, translating security requirements into practical coding practices and championing a security-first mindset within their teams.

A Phased "Crawl, Walk, Run" Implementation
A full-scale DevSecOps transformation can feel daunting. To make the process manageable and build momentum, industry experts like Forrester recommend a phased "Crawl, Walk, Run" approach. This is not just a technical rollout plan; it is a strategic change management initiative that mirrors the classic technology adoption lifecycle. The "Crawl" phase targets the innovators and early adopters on a pilot team, proving the concept. The "Walk" phase is about crossing the chasm to the early majority by standardizing what works. The "Run" phase brings the entire organization into a state of mature, continuous security.
- Phase 1: Crawl (Building Trust and Foundation)
- Assess: Begin with a comprehensive assessment of your current security posture, tools, and processes. The goal is to identify the most significant gaps and weaknesses in your existing CI/CD pipelines and development workflows.
- Pilot: Select a single, relatively low-risk but visible project to serve as your DevSecOps pilot. This is crucial for building trust and demonstrating early wins, proving to skeptical teams that security can be integrated without derailing delivery schedules.
- Automate the Basics: Introduce foundational automated security checks into the pilot team's pipeline. Start with Static Application Security Testing (SAST), which scans raw source code for common flaws, and Software Composition Analysis (SCA), which identifies known vulnerabilities in the open-source libraries your team is using.
- Phase 2: Walk (Scaling Success and Enabling Developers)
- Scale: Take the lessons and successes from your pilot project and begin rolling them out more broadly across the organization. Share the positive results through internal roadshows and testimonials from the pilot team.
- Standardize with "Paved Roads": Create and document "paved roads"—standardized security templates, pre-configured CI/CD pipelines, and libraries of pre-approved, secure components that make it easy for developers to build securely by default. The goal is to make the secure path the path of least resistance.
- Enable: Provide developers with targeted training on secure coding best practices. The objective is not to turn every developer into a security expert, but to equip them with the knowledge to avoid common pitfalls and understand the output of the security tools you've implemented.
- Phase 3: Run (Achieving Continuous Security)
- Advanced Automation: Expand your automated testing capabilities to include more sophisticated techniques. Integrate Dynamic Application Security Testing (DAST), which tests the application while it's running, and Interactive Application Security Testing (IAST), which combines elements of both SAST and DAST for more accurate results.
- Establish Feedback Loops: True continuous security involves learning from the real world. Implement robust monitoring in your production environments and ensure that threat intelligence and performance data are fed back into the development lifecycle to inform and improve future security decisions.
- Become Proactive: Mature DevSecOps practices move beyond simply reacting to vulnerabilities found by scanners. Teams begin to practice proactive threat modeling during the initial design phase, systematically brainstorming how an attacker might target the application and building in defenses before a single line of code is written.
The High Cost of Inaction: Quantifying the Risks of the Status Quo
While implementing DevSecOps requires a strategic investment of time and resources, the cost of inaction is catastrophic. In today's threat landscape, treating security as an afterthought is no longer a calculated risk; it is a direct threat to your financial stability, operational integrity, and brand reputation. The data paints a stark picture of the consequences.
The Financial Fallout of a Breach
The scale of the financial threat from cybercrime is difficult to comprehend. Cybersecurity Ventures predicts that the global cost of cybercrime will reach $10.5 trillion annually by 2025 . To put that in perspective, if cybercrime were a country, it would have the third-largest economy in the world, behind only the United States and China.
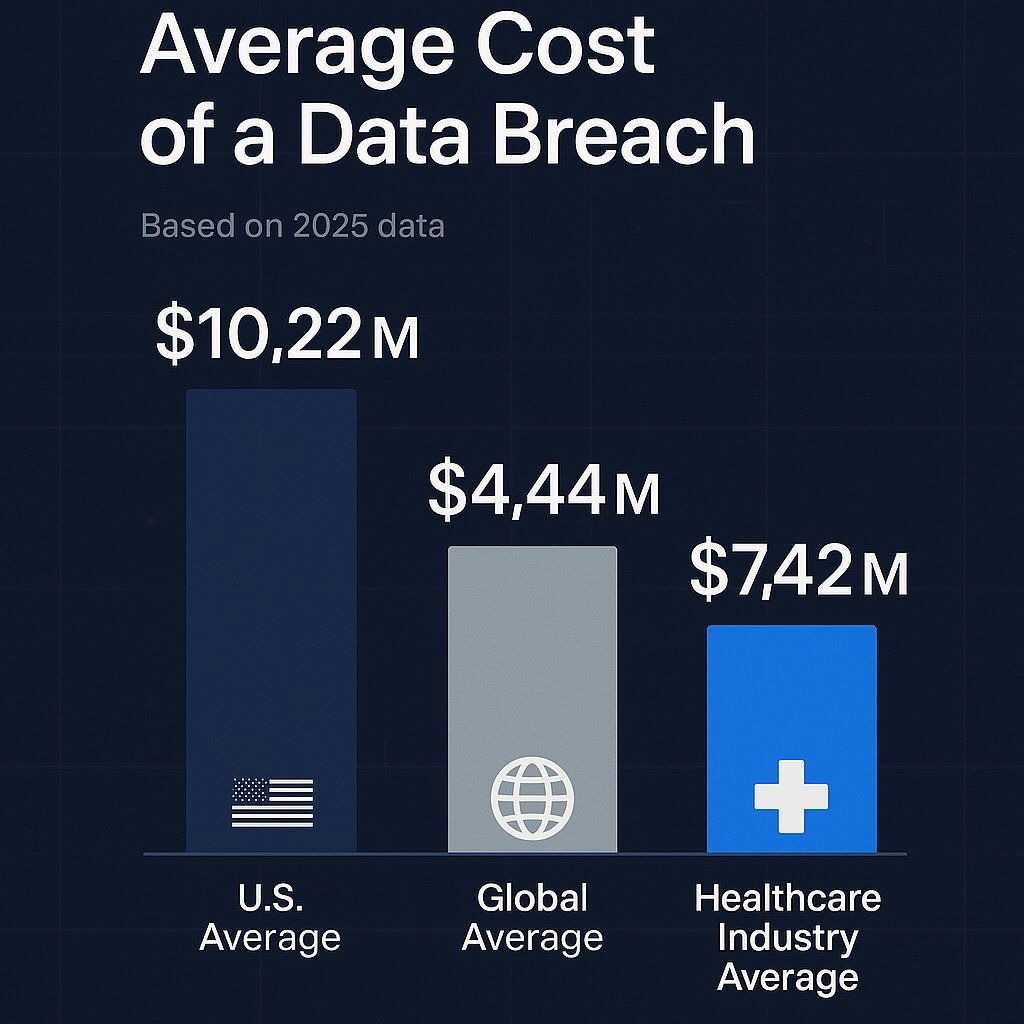
For businesses in the U.S., this global threat has a particularly sharp edge. According to IBM's authoritative 2025 Cost of a Data Breach Report, the average cost of a breach for a U.S. company has surged to an all-time high of $10.22 million —a 9% increase from the previous year and more than double the global average of $4.44 million. This widening gap is not a coincidence. While global breach costs have stabilized, U.S. costs are accelerating, driven by a more punitive regulatory environment and higher costs associated with detection, escalation, and legal action. This creates a disproportionately high "security tax" on U.S. businesses, making proactive security measures not just a best practice, but an urgent financial imperative.
These staggering figures are not just abstract numbers; they are composed of tangible costs that directly impact your bottom line, including detection and escalation, lost business, post-breach response, and customer notification.
Chart: The Escalating Cost of a Data Breach (2025)
This chart illustrates the significant financial disparity in the average cost of a data breach, highlighting the heightened risk for U.S. companies and specific high-risk industries like healthcare.
| Category | Average Cost of Breach |
|---|---|
| U.S. Average | $10.22 million |
| Global Average | $4.44 million |
| Healthcare Industry Average | $7.42 million |
Data sourced from the 2025 IBM Cost of a Data Breach Report.
Beyond the Bottom Line: The Domino Effect of a Security Failure
The direct costs reported by IBM are often just the tip of the iceberg. A significant security failure triggers a cascade of secondary impacts that can cripple a business long after the initial incident is contained.
- Crippling Operational Downtime: When critical systems go offline, the business stops. A single hour of downtime can cost a mid-sized company over $300,000 and a large enterprise $1 million or more in lost revenue, idle employee productivity, and potential penalties for violating Service Level Agreements (SLAs).
- Irreparable Reputational Damage: Trust is the currency of modern business, and a data breach is the fastest way to go bankrupt. Research shows that up to a third of customers in sensitive sectors like retail, finance, and healthcare will simply stop doing business with a company after a breach. Worse, 85% of those affected will share their negative experience with others, with a significant portion taking to social media to amplify their anger. This long-lasting reputational stain makes it incredibly difficult to attract new customers, secure investment, and recruit top talent.
- Crushing Regulatory Penalties: Governments are no longer giving companies a pass on poor security. Landmark regulations like Europe's GDPR and the California Consumer Privacy Act (CCPA) carry severe financial penalties. A serious GDPR violation can result in a fine of up to 4% of a company's annual global turnover or €20 million , whichever is greater. In the U.S., an intentional CCPA violation can cost up to $7,500 per violation —a figure that can quickly escalate into the millions or tens of millions when thousands of customer records are compromised.
These interconnected risks demonstrate that a security breach is not just an IT problem; it is a whole-of-business crisis. To see how a single oversight in AI-driven production software can trigger a domino effect—from financial loss to regulatory scrutiny—study recent real-world AI incidents.
| Risk Category | Specific Examples | Potential C-Suite Impact |
|---|---|---|
| Financial | Incident response costs, regulatory fines (GDPR/CCPA), legal fees, cyber insurance premium hikes. | CFO: Unplanned budget impact, reduced profitability, potential stock price decline. |
| Operational | System downtime, lost sales during outage, employee productivity loss, supply chain disruption. | COO/Head of Sales: Missed revenue targets, SLA breaches, customer service overload. |
| Reputational | Customer churn, loss of brand trust, negative press/social media, difficulty attracting talent. | CEO/CMO: Damaged brand equity, loss of market share, long-term growth impediment. |
| Regulatory | GDPR/CCPA investigations, mandatory disclosures, potential class-action lawsuits. | General Counsel/CEO: Legal liability, personal accountability for leadership, prolonged legal battles. |
Cautionary Tales: Lessons from Three Landmark DevSecOps Failures
Abstract risks and statistics are one thing; real-world failures are another. The following three breaches are not just stories of technical errors. They are strategic failures that serve as powerful case studies on why DevSecOps is essential. Together, they tell a story of escalating complexity, illustrating the evolution of application security risk from basic hygiene to the integrity of the development process itself, and finally, to the vast, hidden landscape of the software supply chain.
Equifax (2017): A Failure of Basic Security Hygiene
The 2017 Equifax breach, which exposed the personal information of over 147 million people, was a masterclass in the failure of fundamental security practices.
- The Story: The attackers did not use a sophisticated, unknown "zero-day" exploit. Instead, they gained entry through a well-known vulnerability in a common open-source framework called Apache Struts. A patch for this vulnerability had been available for two months, and Equifax had even been directly notified of the risk by the Department of Homeland Security. The initial failure to patch was compounded by a series of cascading errors: their own vulnerability scanners failed to detect the unpatched system, and a critical network monitoring device had been inactive for 19 months due to an expired security certificate, rendering them blind as attackers exfiltrated data for 76 days.
- The Impact: The breach ultimately cost Equifax over $1.4 billion in cleanup costs and legal settlements.
- The DevSecOps Lesson: This was a catastrophic failure of automated patching and continuous monitoring . In a mature DevSecOps environment, automated Software Composition Analysis (SCA) tools would have immediately flagged the vulnerable Struts component in the codebase. A robust CI/CD pipeline could have automated the deployment of the patch across all systems, closing the window of opportunity for attackers. Furthermore, effective continuous monitoring would have detected the anomalous network traffic, alerting the security team to the breach in hours or days, not months.
SolarWinds (2020): The Supply Chain Under Siege
The SolarWinds attack represented a paradigm shift in cyberattacks, moving from targeting end-users to compromising the very tools they trust, much like the risks exposed in recent AI-powered software supply chains.
- The Story: This was a highly sophisticated software supply chain attack. State-sponsored hackers infiltrated the internal build environment of the IT management company SolarWinds. They stealthily injected malicious code into the company's flagship Orion software platform. This compromised code was then digitally signed with a legitimate SolarWinds certificate and distributed to thousands of customers as a routine software update. The malware was exceptionally stealthy, designed to lay dormant for weeks and masquerade its network traffic as legitimate Orion activity.
- The Impact: Over 18,000 organizations, including high-level U.S. government agencies like the Pentagon, the State Department, and the Justice Department, installed the trojanized update. The attack cost victim companies an average 11% of their annual revenue .
- The DevSecOps Lesson: The SolarWinds breach is a stark lesson in the need to secure the CI/CD pipeline itself . DevSecOps isn't just about scanning the code you write; it's about ensuring the integrity of the entire software factory. This requires hardening the build environment, implementing strict access controls, and using practices like cryptographic signing for all software artifacts to ensure they haven't been tampered with. It underscores that you must assume even trusted vendor software could be a potential threat vector.
Log4Shell (2021): The Ubiquitous Threat in Open Source
The Log4Shell vulnerability exposed the fragile foundation upon which much of modern software is built. Recent incidents demonstrate how supply chain risks and vulnerabilities in open source dependencies can impact nearly every industry.
- The Story: In late 2021, a critical vulnerability was discovered in Log4j, an open-source logging library for the Java programming language. The flaw was trivial to exploit, allowing for remote code execution, and it received a perfect 10.0 severity score. The true crisis stemmed from Log4j's ubiquity. It was embedded in millions of applications, from enterprise software to cloud services and even video games like Minecraft. The biggest challenge for organizations was that many didn't even know they were vulnerable, as Log4j was often an indirect or "transitive" dependency—a library used by another library their developers had included.
- The Impact: A global, panicked scramble ensued as organizations raced to find and patch every instance of the vulnerable library while attackers immediately began exploiting it to deploy ransomware, cryptominers, and other malware.
- The DevSecOps Lesson: Log4Shell is the ultimate argument for the non-negotiable importance of Software Composition Analysis (SCA) and maintaining a comprehensive Software Bill of Materials (SBOM) . Modern applications are assembled from hundreds of open-source components, and you cannot secure what you don't know you have. A mature DevSecOps practice involves using automated SCA tools to continuously scan all dependencies, map their relationships, and provide immediate alerts when a vulnerability like Log4Shell is discovered anywhere in the software supply chain.
The Modern Defense: Essential DevSecOps Tools and Best Practices
Understanding the risks and learning from past failures is crucial, but the ultimate goal is to build a resilient defense. This requires a combination of foundational principles and a modern toolchain designed to automate security at every stage of the software development lifecycle.

Core Principles for a Secure SDLC
Before diving into specific tools, it's essential to grasp the core principles that underpin a modern, secure development process. For teams embracing new AI-enabled workflows, see how the Agentic SDLC blueprint merges these principles with cutting-edge automation.
- Security as Code (SaC): This principle involves defining and managing your security and compliance policies through code. Instead of manually configuring firewalls or setting user permissions through a UI, you define these rules in configuration files (like YAML or HCL) that are stored in a version control system like Git. This makes your security posture versionable, auditable, and repeatable, eliminating manual errors and configuration drift.
- Continuous Monitoring: Security is not a one-time check. It is an ongoing process that extends long after software is deployed. This involves implementing tools that continuously monitor production environments for active threats, anomalous behavior, and security misconfigurations, providing a constant feedback loop to the development team.
- Immutable Infrastructure: This is a transformative approach to managing infrastructure, particularly in containerized environments. Instead of logging into a running server to apply a patch or change a configuration (a "mutable" approach), you treat the infrastructure as disposable. If an update is needed, you build a new, patched version of the server or container image from a secure base, deploy it, and then destroy the old one. This practice prevents configuration drift and makes your systems far more predictable and resilient.
- Principle of Least Privilege: A foundational concept of Zero Trust security, this principle dictates that any user, application, or system should only have the absolute minimum level of access and permissions necessary to perform its specific function. This dramatically limits the "blast radius" if a component is compromised, preventing an attacker from moving laterally through your network.
Building Your DevSecOps Toolchain
A DevSecOps "toolchain" is not a single product but a set of integrated tools that automate security checks throughout your CI/CD pipeline. In modern cloud-native environments, like the ones we at Baytech Consulting build for our clients using platforms like Azure DevOps and orchestrators such as Rancher with Kubernetes and Docker , these tools are not separate, cumbersome steps. They are woven directly into the fabric of the developer's workflow, providing instant feedback. The strategic goal of this toolchain is to create automated "security gates" that provide a continuous feedback loop to developers. The value is not just in finding flaws, but in finding them early and delivering actionable information back to the person who can fix them instantly. This drastically shortens the Mean Time to Remediation (MTTR), which is a key metric of an effective security program.
| SDLC Stage | Tool Category | Purpose | Examples in a Modern Stack |
|---|---|---|---|
| Plan/Design | Threat Modeling | "Whiteboard" potential attacks and design defenses before coding begins. | OWASP Threat Dragon, Microsoft Threat Modeling Tool. |
| Code | Static Application Security Testing (SAST) & Secret Scanning | Analyzes source code for vulnerabilities and exposed credentials (API keys, passwords) as the developer types. | GitHub Advanced Security for Azure DevOps, SonarQube, Semgrep. |
| Build/Test | Software Composition Analysis (SCA) | Scans open-source dependencies for known vulnerabilities (like Log4j) and license compliance issues. | Snyk, OWASP Dependency-Check, GitHub Advanced Security. |
| Build/Test | Container & IaC Scanning | Scans Docker images and Infrastructure-as-Code (e.g., Kubernetes manifests) for misconfigurations and vulnerabilities. | Trivy, Checkov, Microsoft Defender for Cloud. |
| Staging/Deploy | Dynamic Application Security Testing (DAST) | Tests the running application by simulating real-world attacks to find vulnerabilities that only appear at runtime. | OWASP ZAP, Invicti (Netsparker). |
| Operate/Monitor | Runtime Protection & Monitoring | Monitors production workloads for anomalous behavior and active threats. | Falco, Azure Monitor, Microsoft Defender for Cloud. |
From Risk to Resilience: Your Path Forward
In the face of trillion-dollar cybercrime threats and multi-million-dollar breach costs, clinging to outdated security models is no longer a viable business strategy. DevSecOps is the modern framework for building secure, resilient applications at the speed the market demands. It is not a project with an end date, but an ongoing strategic commitment to excellence.
For business leaders, the path forward is clear and requires decisive action in three key areas:

- Champion the Culture: Lead the charge in transforming your organization's mindset. Make security a shared value and a collective responsibility, breaking down the silos that create friction and risk. For further insight on the organizational strategy, see how operational changes and AI collaboration affect your people and process.
- Invest Strategically: Allocate the necessary resources for the tools and training that enable automation. Focus on building a toolchain that provides fast, actionable feedback to your development teams. Explore more on AI-powered solutions that drive a defensible business advantage in security and automation.
- Start Now, Start Smart: You don't need to boil the ocean. Embrace a phased "Crawl, Walk, Run" approach to build momentum, demonstrate value, and ensure a successful, sustainable transformation. If you’re wondering how to kick-start your organization’s journey, the executive guide to AI integration offers a pragmatic roadmap for business leaders.
The journey from a reactive security posture to a proactive state of resilience is a strategic imperative. It requires vision, commitment, and often, an experienced guide. Firms like Baytech Consulting , with our focus on Rapid Agile Deployment and a Tailored Tech Advantage , specialize in helping businesses navigate this transformation, building the secure, high-performance custom software that drives growth in a complex world.
Further Reading
- Secure Software Development Framework (SSDF) Version 1.1: Recommendations for Mitigating the Risk of Software Vulnerabilities
- 2025 Data Breach Investigations Report | Verizon
- OWASP Top Ten | OWASP Foundation
About Baytech
At Baytech Consulting, we specialize in guiding businesses through this process, helping you build scalable, efficient, and high-performing software that evolves with your needs. Our MVP first approach helps our clients minimize upfront costs and maximize ROI. Ready to take the next step in your software development journey? Contact us today to learn how we can help you achieve your goals with a phased development approach.
About the Author

Bryan Reynolds is an accomplished technology executive with more than 25 years of experience leading innovation in the software industry. As the CEO and founder of Baytech Consulting, he has built a reputation for delivering custom software solutions that help businesses streamline operations, enhance customer experiences, and drive growth.
Bryan’s expertise spans custom software development, cloud infrastructure, artificial intelligence, and strategic business consulting, making him a trusted advisor and thought leader across a wide range of industries.


